Students looking to log in to University of Maryland-run websites will soon have to go through an extra step.
Starting Oct. 15, after students log into these websites, they’ll have to provide a second form of verification, whether inputting a password from an app on their phone or responding to a push notification.
These websites include Testudo, ELMS, MyDRL, MyUHC, Terrapin Express and Library Services.
“There’s a whole spectrum of things we do to protect access to our computing systems,” said Jeff Hollingsworth, the head of this university’s information technology division. “Using just your username and password is no longer efficient.”
The switch to multi-factor authentication was hastened by data breaches at the university, Hollingsworth said, including one from the spring of 2017, wherein a student obtained a professor’s directory ID and password and used it to change grades.
[Read more: The interim head of UMD’s IT division will take over the position full-time]
In 2014, this university was the victim of a major data breach, exposing the names, dates of birth, UIDs, and social security numbers of more than 300,000 students, faculty and staff.
David Morris, a senior English major, said he wished the university was more up front about the need for the authentication, though.
“I would like to know why they’re doing this,” Morris said. “ELMS is already enough of a hassle without having to deal with this.”
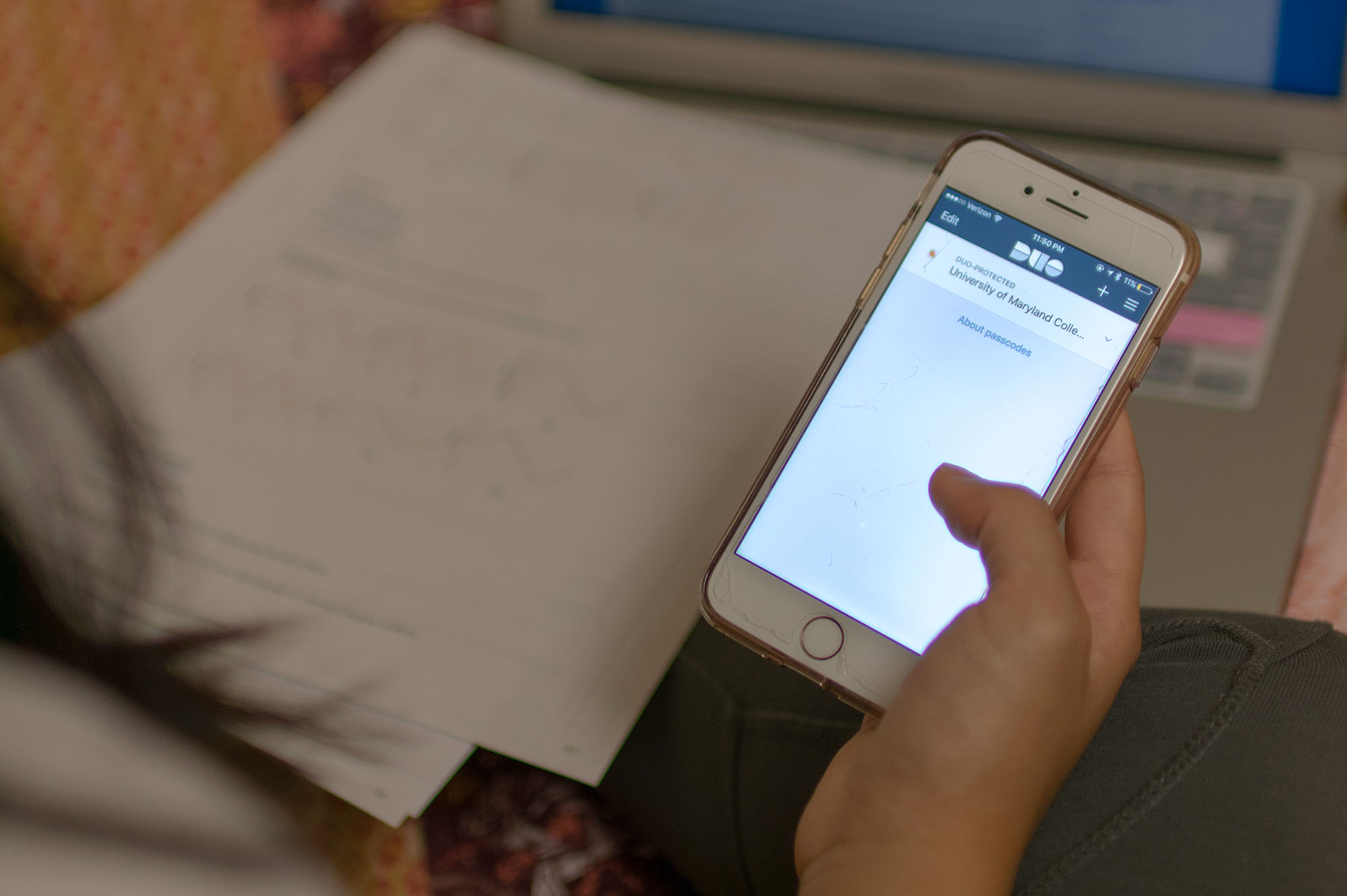
To complete the authentication, students can download the Duo Mobile app on their phones to complete the verification process. After logging in, students will have the option to stay verified for all websites that use the university’s Central Authentication Service on that device for 24 hours, after which they will be prompted to repeat the authentication process.
Yehuda Katz, a computer science graduate student, said he opted into the university’s multi-factor authentication system early to compare it to other verification systems.
“The way the university set it up, it’s not so disruptive,” Katz said. “The vast majority of the time, it’s only once a day, it doesn’t get in the way of anything I’m doing.”
The university’s multi-factor authentication process is licensed through Duo Security, an information security company. Duo’s authentication system is currently in use in tech companies such as Facebook and Yelp, as well as at the University of Michigan.
The university has a $110,000 per year contract with Duo, Hollingsworth said, funded by an increase in student fees and money given by the university to the IT department to improve campus cybersecurity.
[Read more: UMD faculty, students react to the use of plagiarism detection software]
Students without the Duo app or a mobile device can also print out a list of security codes to complete the verification process, or through a $20 “token” that can generate access codes, Hollingsworth said.
The token, similar to a key fob in shape and appearance, will be sold at Terrapin Tech in McKeldin Library, Hollingsworth said.
Hollingsworth said the multi-factor authentication process was gradually rolled out, starting with “key faculty and staff” about three years ago, before adding all faculty in December and all university staff in March.
Michael Hicks, a computer science professor and former director of the university’s cybersecurity center, said while multi-factor authentication would strengthen the university’s data security, he would’ve preferred different reforms.
“What I find … irritating is that the university requires us to change our password every 90 days,” Hicks said. “I would say if the university would do away with anything, they should do away with that.”
Currently, in accordance with state and University System of Maryland guidelines, the university mandates all information technology employees to change their password every 90 days, and all university passwords every 180 days.
In 2016, the chief technologist of the Federal Trade Commission recommended organizations to “consider making other changes to their password policies rather than forcing all users to keep changing their passwords.”
Hollingsworth said the university’s goal is to have all university systems on multi-factor authentication by the summer of 2019, at which point they will petition the state for a waiver to require less frequent password changes.
Hadi Joyowidarbo, a junior economics major, said that given past security breaches at this university, he understands the need.
“If it’s necessary, it’s necessary,” Joyowidarbo said. “If we need it, we need it. Why not?”